IP address search modifiers
VirusTotal Intelligence allows you to perform advanced faceted searches over the historical collection of IP addresses seen by VirusTotal. These searches can act on basically all the metadata generated for IPs: autonomous system, country, whois, SSL certificate, community comments, detections, relationships, etc. For example, you can pivot on SSL certificate fields to try to identify other network infrastructure set up by a given adversary.
VirusTotal Intelligence searches by default over the historical collection of files, in order to search over IPs you need to add the facet condition entity:ip. For example, let's ask for all those IP addresses that have been detected by more than 5 blocklists:
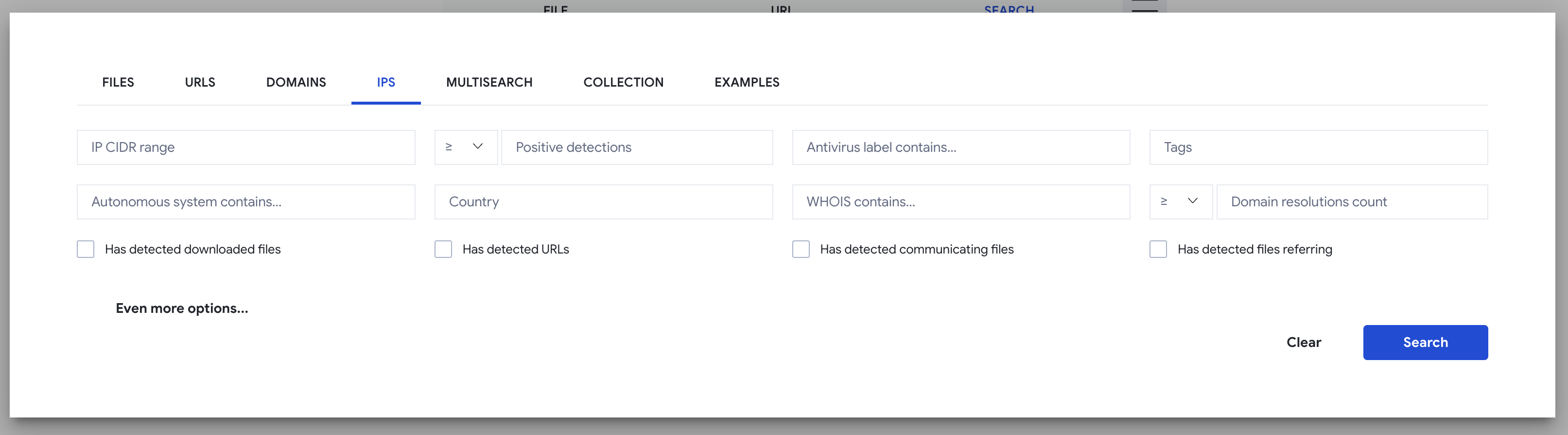
You can click on the filter icon inside the main search box in order to navigate to an IP address search assistant:
Note that the assistant will not allow you to build complex searches combining AND, OR and NOT conditions. For example:
entity:ip positives:5+ AND (aso:ovh OR aso:google)
The following table describes all the search modifiers (facets) that can be used, you can combine any number of them:
| Modifier | Description |
|---|---|
| ip | Narrow down a search to a given IP address range. Example: entity:ip ip:"8.8.8.8/24" |
| asn autonomous_system_number | Narrow down a search to a given autonomous system (by number). Example: entity:ip asn:"15169" |
| aso autonomous_system_owner | Narrow down a search to a given autonomous system (by organization). Example: entity:ip aso:google |
| country | Country where IPs matching a given criteria should be located. ISO ALPHA 2 code required. Example: entity:ip country:us |
| continent | Continent where IPs matching a given criteria should be located. ISO ALPHA 2 code required. Example: entity:ip continent:eu |
| comment | Search for IPs that have a VirusTotal Community comment containing the word or phrase provided. Example: entity:ip comment:phishing |
| comment_author | Search for domains that have been commented by the user with the username provided. Example: entity:ip comment_author:hugoklugman |
| p positives | Filter IPs according to the number of engines/blocklists that detect them. Less than and greater than syntax is allowed. Examples: entity:ip p:5+ |
| engines | Focus on IPs that have a given detection label by at least one blocklist/scanner. Example: entity:ip engines:phishing |
| <engine name> | Focus on IPs that are detected with a given label by a given blocklist/scanner. Example: entity:ip eset:phishing |
| reputation | Filter IPs according to their reputation among the VirusTotal user base. Example: entity:ip reputation:-20- |
| domain_resolutions_count | Search for IPs that have hosted a given number of domains. Accepts greater and less than syntax and saturates at a count of 100. Example: entity:ip domain_resolutions_count:20+ |
| detected_communicating_files_count | Fix a condition based on how many detected files have been seen contacting the given ip when executed in a sandbox. Less than and greater than syntax is allowed but the count saturates at 10. Example: entity:ip detected_communicating_files_count:5+ |
| communicating_files_max_detections | Fix a condition based on the maximum number of detections observed for files that communicate with a given IP. Example: entity:ip communicating_files_max_detections:30+ |
| detected_downloaded_files_count | Fix a condition based on how many detected files VirusTotal has downloaded from a URL hosted under a given IP address. Example: entity:ip detected_downloaded_files_count:10+ |
| downloaded_files_max_detections | Fix a condition based on the maximum number of detections observed for files that were downloaded by VirusTotal from a given IP address. Example: entity:ip downloaded_files_max_detections:20+ |
| detected_referring_files_count | Fix a condition based on how many detected files have been seen containing the given IP address in their strings. Example: entity:ip detected_referring_files_count:10+ |
| referring_files_max_detections | Fix a condition based on the maximum number of detections observed for files that contain a given IP address in their strings. Example: entity:ip referring_files_max_detections:10+ |
| detected_urls_count | Fix a condition based on how many detected URLs have been seen hosted under a given IP address. Example: entity:ip detected_urls_count:10+ |
| urls_max_detections | Fix a condition based on the maximum number of detections observed for URLs hosted under a given IP address. Example: entity:ip urls_max_detections:5+ |
| tag | Filter IPs according to their tags. Example: entity:ip tag:reserved List of available tags: - private: private IP address space, e.g. 192.168.0.1. - multicast: IP address in the multicast range. - link-local: IP valid only for communications within the network segment. - reserved: reserved IP address space. - loopback: IP for the local machine. For a complete list of tags, see Full list of VirusTotal Intelligence tag modifier |
| ssl_issuer | Focus on IPs that contain a given string or fulltext pattern within their SSL certificate issuer field. Example: entity:ip ssl_issuer:"Starfield Secure Certificate Authority - G2" |
| ssl_serial | Focus on IPs that share a given SSL certificate serial field. Example: entity:ip ssl_serial:"99c942e5f4049537" |
| ssl_subject | Focus on IPs that contain a given string or fulltext pattern within their subject field. Example: entity:ip ssl_subject:"naranjamarketing.com" |
| ssl_thumbprint | Focus on IPs sharing a given SSL certificate thumbprint field. Example: entity:ip ssl_thumbprint:62cd39d8b06d1d26e02e7fc8fabe7cb442e08489 |
| whois | Filter IPs according to any word or phrase contained within their Whois record. Example: entity:ip whois:"Hurricane Electric LLC" |
| have | Allows you to fix a condition that the IP’s indexed metadata should meet, it accepts any of the modifiers above and it means that the IP should have data for a given modifier. Example: entity:ip have:comment |
| last_modification_date lm | Filter IPs based on the latest update on VirusTotal for IP. Example: entity:ip last_modification_date:3d+ |
| jarm | Filter IPs based on the JARM fingerprint. Example: entity:ip jarm:29d3fd00029d29d21c42d43d00041d188e8965256b2536432a9bd447ae607f |
| ssl_not_before | Filter IPs based on the start date of the last SSL certificates' validity. Example: entity:ip ssl_not_before:2023-10-01 |
| ssl_not_after | Filter IPs based on the end date of the last SSL certificates' validity. Example: entity:ip ssl_not_after:2023-10-01 |
| threat_actor related_actor | Filter IPs which have that related threat actor. Example: entity:ip threat_actor:apt29 |
Updated 5 months ago
